Use your exploitation skills to bypass authentication mechanisms on a website and get RCE.
Write-up: Hammer


Use your exploitation skills to bypass authentication mechanisms on a website and get RCE.

The librarian rushed some final changes to the web application before heading off on holiday. In the process, they accidentally left sensitive information behind! Your challenge is to find and exploit the vulnerabilities in the application to extract these secrets.
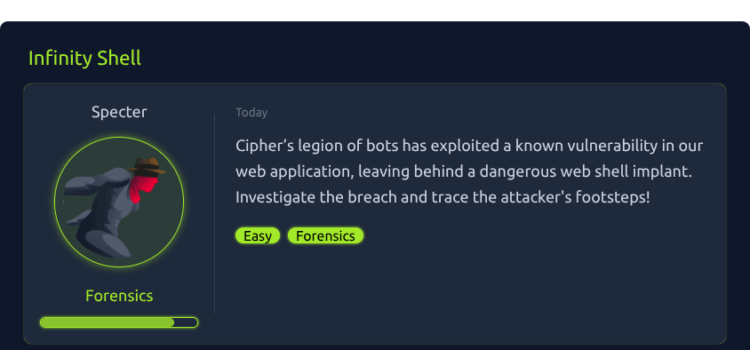
Cipher’s legion of bots has exploited a known vulnerability in our web application, leaving behind a dangerous web shell implant. Investigate the breach and trace the attacker’s footsteps!

Building multiplatform Docker images in GitHub Actions often requires custom Docker daemon configurations, but these can introduce unexpected issues. This article explores a common pitfall with Docker contexts when using the containerd image store feature, particularly when running security scans with tools like Trivy. Learn how to extract and pass the correct Docker socket to ensure seamless integration and accurate vulnerability scans.
In this blog post, we explore the process of configuring Renovate to automatically update DevContainer images. Development containers offer lightweight, portable development environments, defined through a devcontainer.json file. However, manually updating image references within this file can be tedious and error-prone.
We delve into how Renovate, an automated dependency update tool, can be tailored to handle DevContainer files efficiently. By leveraging Renovate’s custom managers and flexible template system, developers can seamlessly manage DevContainer image updates, enhancing workflow efficiency and reducing manual overhead.

Development Containers represent a paradigm shift in software development methodology, encapsulating comprehensive development environments within containerized configurations. This approach addresses the imperative need for consistency across diverse development environments by packaging essential tools, libraries, and configurations within self-contained units. Developers can utilize DevContainers to seamlessly share and replicate their development setups, fostering collaboration and enabling a hassle-free onboarding process for new team members. This enhances efficiency, reduces setup time, and mitigates compatibility issues, ultimately streamlining the development workflow.
The DevContainers CLI is a robust command-line interface integral to managing and manipulating development containers. However, nothing is bug-free, and this post details a troubleshooting experience with the DevContainers CLI to build development multi-architecture development container images with embedded features.
The January 2024 release of VSCode brought a noteworthy update – support for the “Hey Code” voice command. This new feature allows users to interact with Visual Studio Code using voice commands.
I decided to try it.

Codespace environments are backed with development containers (dev containers for short). They are supported by other tools, for example, Visual Studio Code.
And even though Microsoft maintains both Dev Containers extension for VSCode and GitHub Codespaces, they behave differently in some aspects.
This article shows one of the bugs, which is related to Automatic Port Forwarding.

This article explains how to set up a codespace to allow for signing git tags.

This post explains how to emulate a real request in a WP CLI shell so that all global variables are populated correctly — the same way as if you requested that URL in the browser.