This story was told by my colleague. She had a CentOS 7 server with a bunch of WordPress installations, and she needed to update them all. She obviously did not want to do that manually and preferred to use wp-cli. The system had rkhunter installed.
CentOS does not have `/usr/local/bin` in `PATH`, and that is why she installed `wp-cli` as `/usr/bin/wp` (`wp` is the common name for the installed `wp-cli` script and is suggested by the official installation guide).
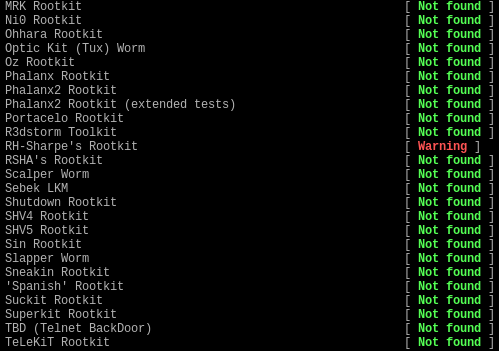
The most interesting happens when rkhunter is run: it complains that the system could be infected with RH-Sharpe’s Rootkit:
In the logs we see something like this:
[18:37:03] Checking for RH-Sharpe's Rootkit... [18:37:03] Checking for file '/bin/lps' [ Not found ] [18:37:03] Checking for file '/usr/bin/lpstree' [ Not found ] [18:37:03] Checking for file '/usr/bin/ltop' [ Not found ] [18:37:03] Checking for file '/usr/bin/lkillall' [ Not found ] [18:37:03] Checking for file '/usr/bin/ldu' [ Not found ] [18:37:03] Checking for file '/usr/bin/lnetstat' [ Not found ] [18:37:03] Checking for file '/usr/bin/wp' [ Found ] [18:37:03] Checking for file '/usr/bin/shad' [ Not found ] [18:37:03] Checking for file '/usr/bin/vadim' [ Not found ] [18:37:03] Checking for file '/usr/bin/slice' [ Not found ] [18:37:03] Checking for file '/usr/bin/cleaner' [ Not found ] [18:37:03] Checking for file '/usr/include/rpcsvc/du' [ Not found ] [18:37:03] Warning: RH-Sharpe's Rootkit [ Warning ] [18:37:03] File '/usr/bin/wp' found
I was a bit surprised that rkhunter had not examined the suspicious file further, but according to rkhunter’s README, this is the expected behavior:
– Path-based means RKH will check for filenames. It does not include or use heuristics or signatures like for instance an antivirus product could. Do understand that the SCANROOTKITMODE configuration option and “suspscan” functionality are just crude attempts to try and bridge that gap.
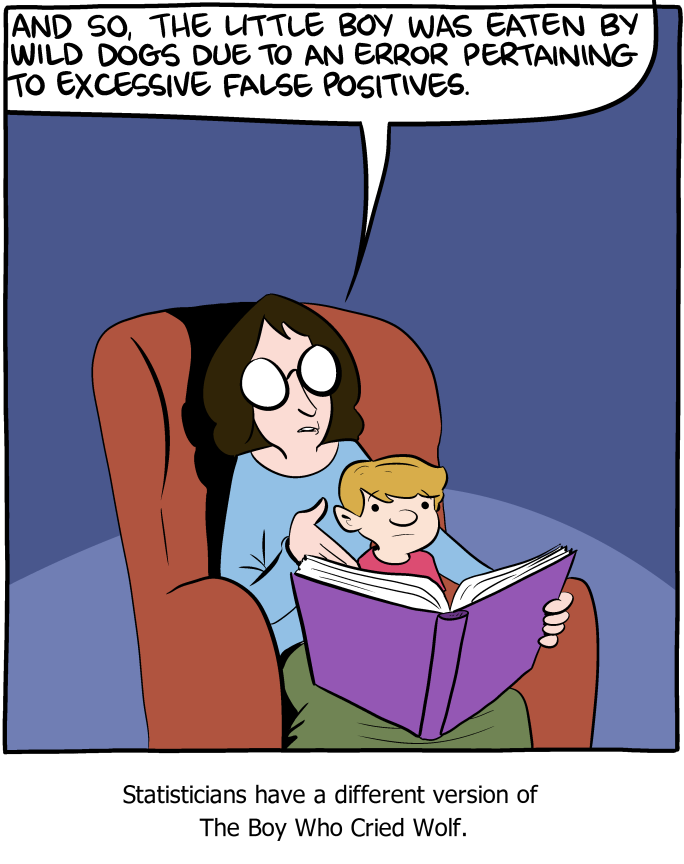
I cannot say I like this: in my opinion, false positives are a dangerous thing, because a tool which produces too many false positives will be treated just like the boy who cried wolf.
Update: the log above also mentions `/usr/bin/slice`, which can be a legitimate script (a part of `slice` package in Ubuntu) and can also trigger a false positive.
Conclusions:
- Be careful with rkhunter, as it can be very inaccurate.
- If you need to install `wp-cli` on CentOS, `/usr/bin/wp` could be a bad choice (you will need to whitelist the script in rkhunter’s configuration file).